Welcome to our deep dive into the April 14, 2026, security release. Microsoft just dropped its second-largest monthly batch of fixes on record, addressing a staggering 165 vulnerabilities. This month isn’t just about volume—though with 165 vulnerabilities addressed, it is officially Microsoft’s second-largest Patch Tuesday on record—it’s about a fundamental shift in the threat landscape.
As we move through the second quarter of 2026, two themes dominate: the rapid acceleration of vulnerability discovery powered by agentic AI and the ticking clock toward a critical Secure Boot deadline.
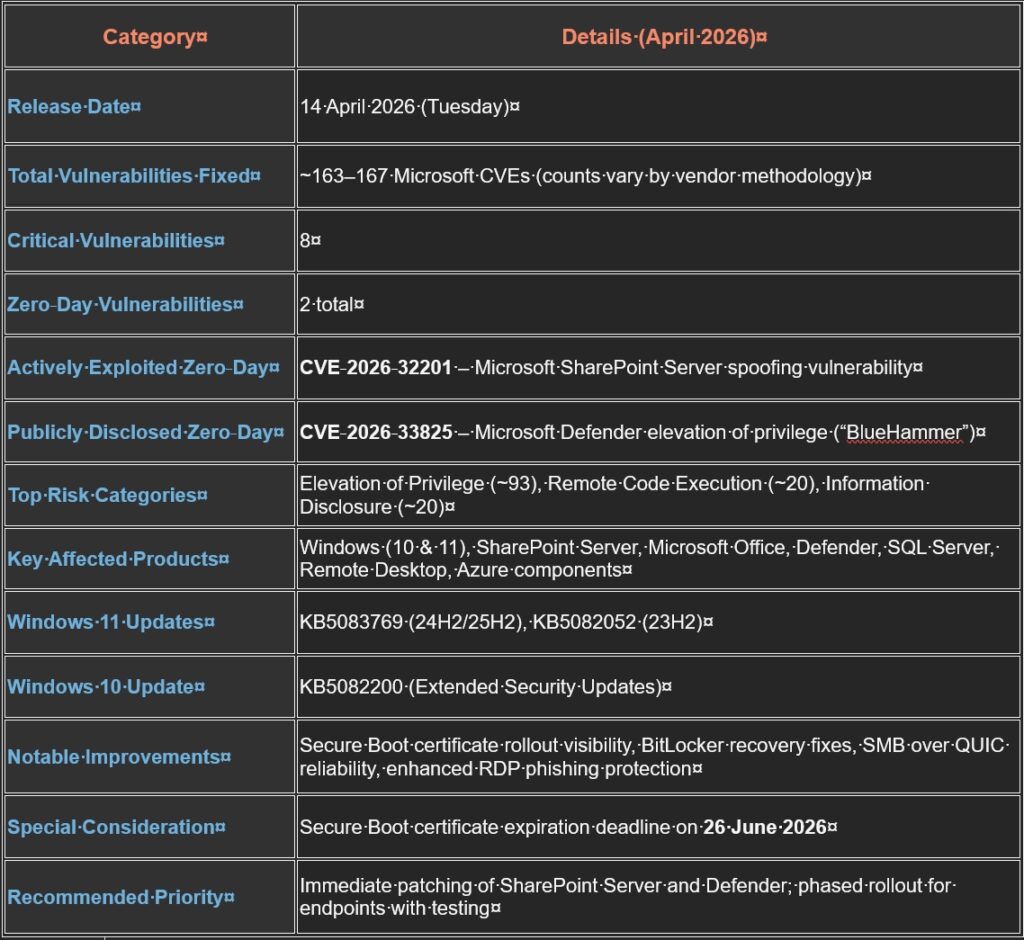
The April 2026 Snapshot
This month, the sheer scale of fixes reflects an industry-wide uptick in reports, largely credited to AI-driven discovery tools that can probe codebases 10x faster than traditional methods.
- Total CVEs: 165
- Critical Vulnerabilities: 8
- Actively Exploited (Zero-Day): 1 (CVE-2026-32201)
- Publicly Disclosed: 1 (CVE-2026-33825)
- Browser-Specific Fixes: 60+ (A new record for Edge/Chromium in a single cycle)
Critical Priorities: What to Patch First
1. The Active Spoofing Zero-Day (CVE-2026-32201)
Targeting Microsoft SharePoint Server, this vulnerability allows unauthenticated attackers to spoof content over the network.
- The Threat: Attackers can deceive users within trusted SharePoint environments, presenting falsified information or modifying sensitive data.
- Action: Admins of on-premises SharePoint 2016, 2019, or Subscription Edition must prioritize this immediately.
2. The “BlueHammer” Defender Exploit (CVE-2026-33825)
This Elevation of Privilege (EoP) bug in Microsoft Defender was publicly disclosed—with exploit code published on GitHub—before a patch was ready.
- The Threat: It allows a local attacker with low privileges to escalate to SYSTEM level.
- Note: While Defender usually updates automatically, managed enterprise environments should verify that the Antimalware Platform version is updated.
3. High-Risk Wormable RCEs
Two vulnerabilities stand out for their potential to self-propagate:
- CVE-2026-33824 (Windows IKE): A Critical (9.8 CVSS) Remote Code Execution vulnerability in Internet Key Exchange extensions. Attackers can hit any system with IKEv2 enabled by sending crafted packets—no user interaction needed.
- CVE-2026-33827 (Windows TCP/IP): A race condition that enables RCE via specially crafted IPv6 packets.
The Secure Boot "Crisis" Countdown
April marks a critical milestone for the Secure Boot certificate expiration. The original 2011 certificates expire on June 26, 2026—just 73 days away.
- New Visual Cues: Starting this month, the Windows Security app (under Device Security > Secure Boot) will display status badges. A green checkmark means you’re updated; yellow or red indicates your hardware requires manual firmware intervention before the June cutoff.
- The Risk: Systems that aren’t updated by late June will enter a “degraded security state,” losing protection against sophisticated bootkit malware like BlackLotus.
Strategic Advice for IT Admins
Given that March 2026 saw several update quality issues (including the pulled KB5079391), April requires a balanced approach.
- Phase Your Rollout: Use Windows Autopatch to pilot updates on non-critical systems first.
- Verify Secure Boot: Use PowerShell (Get-SecureBootUEFI -Decoded) to confirm your fleet is ready for the June certificate rotation.
- Watch the AI Gap: Attackers are using agentic AI to reverse-engineer these patches within minutes. The “Exploit Wednesday” window has shrunk to hours, so automate your critical server patching where possible.
- Action Item: If you are running legacy systems, remember that Windows 10 Enterprise LTSB 2016 reaches End of Support on October 13, 2026. Use this massive update cycle to audit your migration progress.
Summary Table of the Vulnerabilities Addressed in Microsoft Patch Tuesday – April 2026
Final Thoughts
Staying secure in 2026 is becoming a high-volume job. Ensure your automated patch management systems are firing correctly, and don’t wait for “Exploit Wednesday” to secure your perimeter.
At Dual Layer managed IT services, we have developed automated patching plans to suit the client needs. Connect with us to learn more about software updates patching practices.

