Why Your Business Needs Managed Automation Now
TLS/SSL certificates are the foundation of secure internet communication. They protect websites, applications, email systems, VPNs, and APIs by encrypting data and proving identity. However, the way certificates are managed is about to change dramatically.
The CA/Browser Forum—the standards body behind Chrome, Safari, Edge, and Firefox—has approved a mandatory reduction of public TLS certificate lifetimes, shrinking them from today’s 398 days to just 47 days over the next few years.
For businesses, this is more than a technical adjustment. It is an operational risk that, if not handled correctly, can cause unexpected outages, compliance failures, and lost customer trust.
What Is Changing?
Currently, most public TLS certificates are valid for just over one year. That maximum lifetime is being reduced in phases:
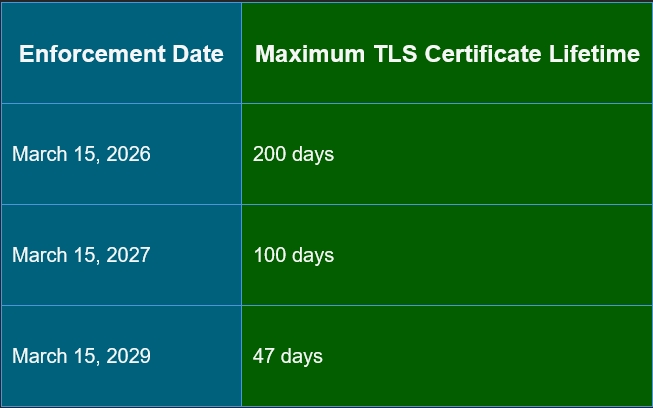
After each enforcement date, browsers will reject certificates that exceed the new maximum validity.
In simple terms:
Certificates will need to be renewed every month by 2029.
Domain Validation Is Also Tightening
In addition to shorter lifetimes, the reuse window for domain validation (DCV) is shrinking:
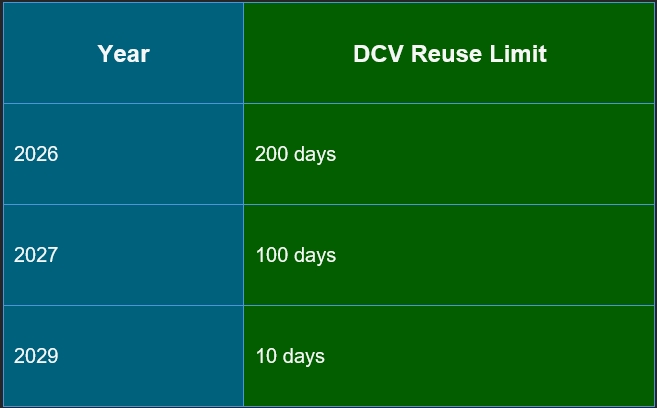
This means businesses will need to prove they control their domains far more frequently, making manual processes unrealistic.
Why the Industry Is Enforcing This Change
Major browser vendors—including Apple, Google, Microsoft, and Mozilla—unanimously supported this change for several reasons:
- Improved Security: Short‑lived certificates drastically reduce the damage window if a certificate or private key is compromised.
- Less Reliance on Revocation: Certificate revocation mechanisms (CRL, OCSP) are inconsistent. Short lifetimes reduce reliance on revocation entirely.
- Faster Adoption of Stronger Encryption: As cryptographic standards evolve (including preparation for post‑quantum cryptography), frequent certificate replacement makes upgrades easier.
- Automation by Design: Manual certificate tracking has long been a leading cause of outages. This change forces organizations to adopt automation and modern lifecycle management.
What This Means for Businesses
Without proper automation, organizations face:
- Missed renewals and service outages.
- Website downtime and browser trust errors.
- Broken APIs, email, and SaaS integrations.
- Increased compliance and audit findings.
- Higher operational overhead for IT teams.
By 2029, manual certificate management is no longer viable, even for small environments.
What Is Not Changing (Good News)
- Existing certificates remain valid until they naturally expire.
- Private/internal PKI certificates are not affected.
- Multi‑year subscriptions still exist (certificates are simply re‑issued more often).
The challenge is not cost; it is process and operational readiness.
Why Managed Services Are the Right Approach
Certificate lifecycle management is becoming a 24/7 automated security function, not an occasional admin task.
- Automated Certificate Renewals: With standards like ACME (Automatic Certificate Management Environment), certificates are issued, renewed, and deployed automatically, without human intervention.
- Centralize Certificate Visibility: Track all certificates across websites, load balancers, firewalls, cloud platforms, and SaaS integrations.
- Eliminate Downtime Risk: Proactive monitoring ensures certificates are replaced before expiration, every time.
- Meet Compliance and Audit Requirements: Short‑lived certificates align with zero‑trust, ISO 27001, SOC 2, and financial services requirements.
The Bottom Line
TLS certificates are no longer “set and forget.” They are now short‑lived security credentials that require continuous automation and monitoring.
Businesses that act early will experience:
- Fewer outages.
- Stronger security posture.
- Lower long‑term operational risk.
Those that delay will experience certificate failures the hard way, during peak business hours.
How We Can Help
As a Managed Service Provider, we help clients with:
- Automated TLS certificate issuance and renewal.
- Multi‑vendor and multi‑cloud support.
- DNS‑based validation automation.
- Centralized monitoring and reporting.
- Incident response for certificate‑related outages.
If you’re unsure how this change affects your environment, our managed IT services team can assess your current certificate footprint and build an automation plan tailored to your business.
Ensure your infrastructure is ready before browser enforcement makes the decision for you.

