Microsoft’s May 2026 Patch Tuesday delivers a large release covering 120+ CVE-numbered issues across Windows, Office, Hyper-V, DNS Client, Netlogon, .NET, and other platforms; Microsoft notes the release is on the larger side and attributes much of the discovery volume to expanded AI-assisted scanning and broader researcher participation. Vendors and industry analysts report this month contains no publicly observed zero-days at release time, but multiple issues are flagged as higher priority due to exploitability characteristics and broad attack surface.
What matters most (high-level)
- Remote-document RCEs in Microsoft Word (multiple CVEs) are highlighted as top priorities because they can be triggered by simply viewing a malicious document in preview panes or mail clients, increasing likelihood of mass exploitation.
- A pre-auth stack-based buffer overflow in Netlogon (CVE-2026-41089) has domain-controller impact and is recommended to be patched across all DCs in the same maintenance window to avoid mixed-state risks.
- A DNS Client remote code execution vector (CVE-2026-41096) can be triggered by malicious DNS responses and affects most Windows hosts that issue DNS queries, making it widely relevant across enterprises.
- A Hyper-V guest-to-host elevation (CVE-2026-40402) should be treated as high priority for multi-tenant hosts or environments running untrusted guests.
- Microsoft’s guidance encourages triage by exposure and impact rather than raw counts, and reiterates fundamentals; timely patching, exposure reduction, identity hygiene, segmentation, and detection/response improvements.
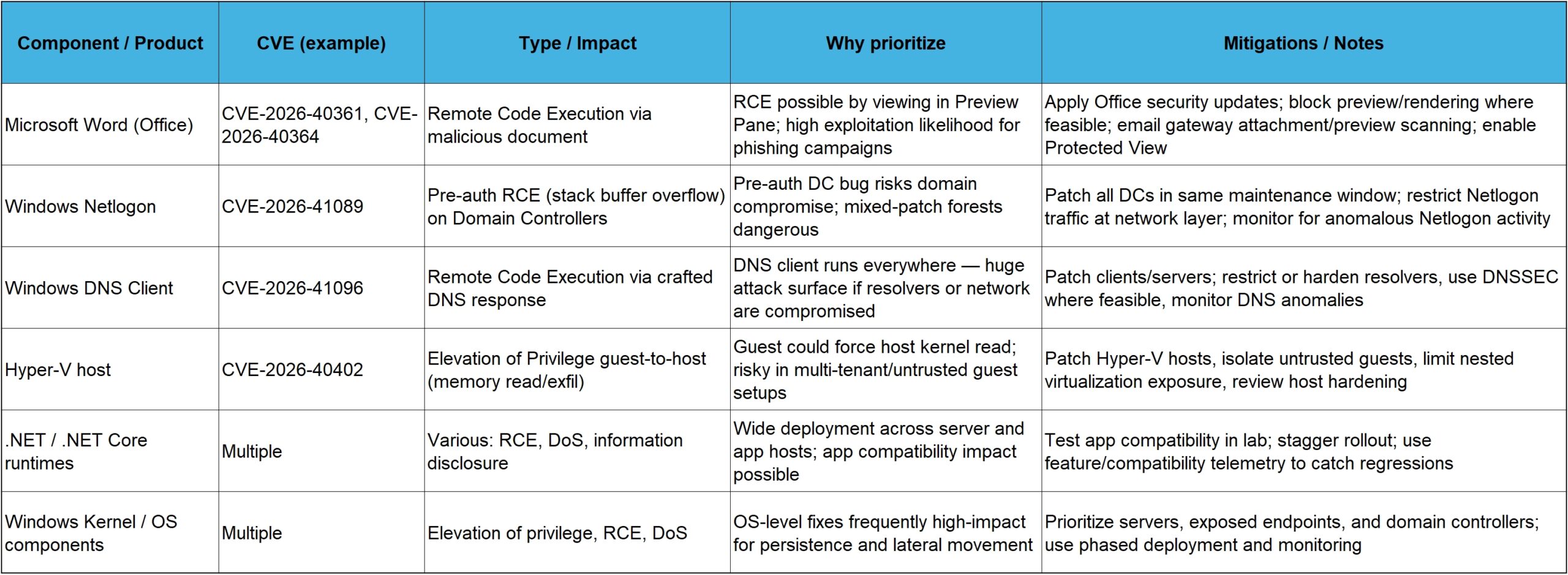
Summary table — notable May 2026 fixes
Patch prioritization and rollout strategy (technical)
- Inventory & exposure-first triage: Map vulnerable components to internet-facing systems, critical servers (DCs, mail, identity), and multi-tenant hosts; prioritize those with pre-auth or unauthenticated RCEs first.
- Domain controllers: Schedule a single maintenance window to patch all DCs and avoid half-patched forests in the case of Netlogon/DC-impacting fixes.
- Virtualization hosts: Apply Hyper-V updates promptly on hosts with untrusted or externally provisioned guests and consider temporarily pausing migration/placement of untrusted guests until patched.
- Endpoint/homogeneous rollout: Stage updates via rings (pilot → broad), but accelerate rings that include high-exposure devices (VPN gateways, admin workstations, helpdesk systems). Use feature rollback plans and telemetry to detect regressions.
- Application compatibility: Test .NET and Office updates against critical line-of-business apps in a pre-prod environment; if immediate patching risks availability, compensate with network/identity mitigations and monitoring.
- Network mitigations: Restrict Netlogon traffic, harden DNS resolver configuration, deploy egress filtering and DNSSEC, and consider additional gateway scanning for document attachments.
- Detection & response: Add signatures/eta hunts for suspicious Netlogon/DNS/Office exploit indicators and validate EDR coverage on privileged endpoints and hosts.
Known issues and operational considerations
Large release volumes mean a higher chance of regressions; monitor vendor advisories and community channels (sysadmin forums and vendor release notes) for early reports of breakages.
- Out-of-band updates: Microsoft says out-of-band patches will remain reserved for urgent cases but customers should expect larger monthly releases as AI scanning surfaces more issues.
- Patch telemetry: Use Windows Update for Business, WSUS, SCCM/ConfigMgr, or Intune to control rollout; ensure visibility into devices that fail to update and prioritize remediations there.
Short checklist for the week (practical)
- Identify systems with exposed Netlogon or DNS-facing roles and schedule immediate patching.
- Move all domain controllers into one maintenance round and deploy Netlogon DC fixes together.
- Patch Hyper-V hosts hosting untrusted or external VDI guests immediately.
- Deploy Office/Word updates to mail gateways and endpoints; disable preview panes where organizationally acceptable until patches are applied.
- Test and stage .NET runtime updates for app compatibility; if needed, isolate affected apps behind compensating controls.
- Update IR/monitoring playbooks to detect indicators tied to the patched CVEs and monitor Windows Update and vendor channels for later advisories.
At Dual Layer managed IT services, we have developed automated patching plans to suit the client needs. Connect with us to learn more about software updates patching practices.

